Tag: malware

QR code phishing: What MSPs need to know to protect their customers
In today’s digital age, the use of technology continuously evolves to make our personal and professional lives more convenient. Quick Response (QR) code has been one such advancement. This two-dimensional barcode allows users to share website URLs and contact information...

How attackers weaponize generative AI through data poisoning and manipulation
The generative AI models that today power chatbots, online search queries, customer interactions, and more are known as large language models (LLMs). The LLMs are trained on vast volumes of data and then use that data to create more data,...

Tech Time Warp: The wicked ways of the Witty Worm
Although the goal of the Witty Worm wasn’t widespread damage—its entire target population was only 12,000 computers the world over—the malware made its presence known with a vengeance. Within 45 minutes of its first appearance at approximately 8:45 p.m. PST...

Cybersecurity Threat Advisory: StrelaStealer malware targets organizations
A new email threat, StrelaStealer malware, is targeting Europe and United States organizations. It spreads through phishing emails with attachments that execute its dynamic-link library (DLL) payload designed to steal email login data. This Cybersecurity Threat Advisory reviews the threat...

Tech Time Warp: Magistr “disembowels” computers
In early 2001, a nasty bug began making the rounds, hitting computer users hard with a particularly challenging payload as seen in this edition of Tech Time Warp. Magistr—sometimes called “Disemboweler” after the Swedish hacker group thought to be behind...

Five ways cybercriminals use AI to wreak havoc
It seems that each time there is a new technology advancement, criminals quickly cut to the front of the line when it comes to dreaming up new applications. That is the case with generative artificial intelligence (AI), which has been...

MSPs have an opportunity to change the cybersecurity game
For as long as anyone can remember, cybersecurity has been a game of whac-a-mole where resources are hopefully marshaled in time to thwart a threat either before damage is inflicted or, at the very least, as quickly as possible once...
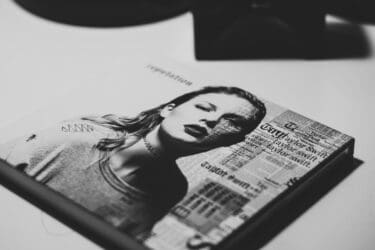
Swifties can pose cyber risks
If you are like me, the whole Taylor Swift-Travis Kelce romance isn’t keeping you up at night. Taylor Swift can be an economic boom to cities where she tours, but she can also be an unintentional cyber risk to her legions...

Scattered Spider spins a troublesome web
The Itsy-Bitsy Spider may have crawled up the waterspout, but the Scattered Spider could be crawling into your email box. CISA is sounding the alarm about Scattered Spider and the havoc it can wreak. The CISA bulletin says: “Scattered Spider...

